Results 1,001 to 1,025 of 1086
Thread: *** The Security News Thread ***
-
08-04-2021, 02:48 AM #1001Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
-
08-04-2021, 11:49 AM #1002
And now LinkedIn...
Data scraped from 500 million LinkedIn users found for sale online
https://www.techrepublic.com/article/data-scraped-from-500-million-linkedin-users-found-for-sale-online/
-
09-04-2021, 09:01 AM #1003Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Pwn2Own 2021: Microsoft Exchange Server, macOS, Windows 10 and Teams HackedPwn2Own 2021: Microsoft Exchange Server, macOS, Windows 10 and Teams Hacked
Winners of the first day have earned more than half a million already.
-
13-04-2021, 05:45 PM #1004
Probably by design....
Joker malware infects over 500,000 Huawei Android devices
More than 500,000 Huawei users have downloaded from the companys official Android store applications infected with Joker malware that subscribes to premium mobile services.
Researchers found ten seemingly harmless apps in AppGallery that contained code for connecting to malicious command and control server to receive configurations and additional components.
A report from antivirus maker Doctor Web notes that the malicious apps retained their advertised functionality but downloaded components that subscribed users to premium mobile services.
To keep users in the dark the infected apps requested access to notifications, which allowed them to intercept confirmation codes delivered over SMS by the subscription service.
According to the researchers, the malware could subscribe a user to a maximum of five services, although the threat actor could modify this limitation at any time.
The list of malicious applications included virtual keyboards, a camera app, a launcher, an online messenger, a sticker collection, coloring programs, and a game.
Joker malware infects over 500,000 Huawei Android devices
-
13-04-2021, 06:11 PM #1005
Malicious code in APKPure app
Recently, we’ve found malicious code in version 3.17.18 of the official client of the APKPure app store. The app is not on Google Play, but it is itself a quite a popular app store around the world. Most likely, its infection is a repeat of the CamScanner incident, when the developer implemented a new adware SDK from an unverified source.
We notified the developers about the infection on April 8. APKPure confirmed the issue and promptly fixed it with the release of version 3.17.19.
Malicious code in APKPure app | Securelist
-
22-04-2021, 04:02 AM #1006Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Another "dating service“ hack. If you are still in the closet, this could be a problem.
"Men's social networking website and online dating application Manhunt has suffered a data breach.
According to a security notice, the 20-year-old site was compromised in a cyber-attack that took place in February 2021.
An unauthorized third party downloaded personal information belonging to some Manhunt users after gaining access to the company's account credential database.
The compromised database contained customers' usernames, email addresses, and passwords. After discovering that a breach had occurred, Manhunt performed a forced reset of all users' passwords.
Manhunt began notifying users of the security incident last month. The company did not say how many of the approximately 6 million men who use the site had been impacted by the attack."
Dating Service Suffers Data Breach - Infosecurity Magazine
-
22-04-2021, 04:35 AM #1007Banned





















- Join Date
- Apr 2020
- Last Online
- 29-01-2022 @ 06:16 AM
- Location
- the mask freedom zone
- Posts
- 1,844
^Have you warned snubby and antsy about it yet?

-
23-04-2021, 01:14 AM #1008Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
-
01-05-2021, 08:09 AM #1009Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Careful where you click...
https://ciso.economictimes.indiatime...aders/82324228In perhaps one of the biggest phishing incidents targeting some of the world’s largest news organizations, hackers have created fake replica websites of news portals of 900 global news portals, including at least 57 from India including websites of The Hindu, NDTV, Hindustan Times, and News18 among many others and are using them to distribute malware and scam advertisements.
Other affected news portals include those belonging to Jagran, Moneycontrol, DNA, Punjab Kesari, Jan Satta, First Post and Business Standard. Global news portals that were targeted include portals of BBC, Washington Times, and The Australian among several others.
-
01-05-2021, 08:40 AM #1010
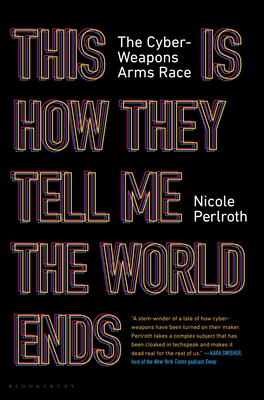
if you are really interested in computer and online security
you should read this and stop installing appliances on your edge - build only exactly what is needed
This Is How They Tell Me the World Ends: The Cyberweapons Arms Race by Nicole Perlroth
https://www.goodreads.com/book/show/...SE4UQzz&rank=1
-
03-05-2021, 04:14 PM #1011
Not a lot of explanation there Baldrick. Has Zero Trust gone out of the window now then?
-
04-05-2021, 02:31 PM #1012
ZTNA is useless if you are trusting vendor appliances
Build your appliances yourself with an OS and applications that you can trust . It seems the zero days seem to be mainly available for vendor devices.
Not withstanding your users opening doc files
-
05-05-2021, 04:02 PM #1013
Chinky bastards at it again.
Chinese TV maker: Yes, our Android TVs spied on customers [updated] | Tom's Guide
-
09-05-2021, 06:43 AM #1014Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Appears that a Chinese company is behind a "a major coordinated scheme by Amazon vendors to procure fake reviews for their products."
Misconfigured Database Exposes 200K Fake Amazon Reviewers - Infosecurity Magazine
-
29-05-2021, 09:42 PM #1015
Chinky bastards at it again.
Chinese cyberspies are targeting US, EU orgs with new malwareChinese threat groups continue to deploy new malware strains on the compromised network of dozens of US and EU organizations after exploiting vulnerable Pulse Secure VPN appliances.
As FireEye threat analysts revealed last month, state-sponsored threat actors were exploiting a recently patched zero-day in the Pulse Connect Secure gateways.
After compromising the targeted devices, they deployed malware to maintain long-term access to networks, collect credentials, and steal proprietary data.
"We now assess that espionage activity by UNC2630 and UNC2717 supports key Chinese government priorities," FireEye said in a follow-up report published on Thursday.
"Many compromised organizations operate in verticals and industries aligned with Beijing's strategic objectives outlined in China's recent 14th Five Year Plan."
-
01-06-2021, 06:04 PM #1016
Might be a good time to buy shares in Tyson Foods...
Food giant JBS Foods shuts down production after cyberattackJBS Foods, a leading food company and the largest meat producer globally, had to shut down production at multiple sites worldwide following a cyberattack.
The incident impacted multiple JBS production facilities worldwide over the weekend, including those from the United States, Australia, and Canada.
JBS is currently the world's largest beef and poultry producer and the second-largest global pork producer, with operations in the United States, Australia, Canada, the United Kingdom, and more.
The company has a team of 245,000 employees around the world, serving an extensive portfolio of brands including Swift, Pilgrim's Pride, Seara, Moy Park, Friboi, Primo, and Just Bare to customers from 190 countries on six continents.
-
02-06-2021, 04:41 AM #1017Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
-
07-06-2021, 10:34 PM #1018Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Seems the US is starting to take Ransomware seriously now:
US to Treat Ransomware Like Terrorism: US to Treat Ransomware Like Terrorism - Infosecurity Magazine
-
08-06-2021, 01:51 PM #1019
-
09-06-2021, 02:02 AM #1020Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Ah, I remember those from years ago. As a teen, I'd fill the whole thing out. Bad choices.
-
09-06-2021, 02:25 AM #1021Member































- Join Date
- Jan 2020
- Last Online
- 01-08-2023 @ 11:33 PM
- Posts
- 510
Looks like we aren't going to see an end to price increases and supply shortages any time soon.
Cyberattacks on Transportation and Logistics System Witness a Surge
https://cyware.com/news/cyberattacks...surge-10d94d2b
-
14-06-2021, 12:25 PM #1022
Audi and Volkswagen have suffered a data breach affecting 3.3 million customers after a vendor exposed unsecured data on the Internet.
Volkswagen Group of America, Inc. (VWGoA) is the North American subsidiary of the German Volkswagen Group. It is responsible for US and Canadian operations for Volkswagen, Audi, Bentley, Bugatti, Lamborghini, and VW Credit, Inc.
According to data breach notifications filed with the California and Maine Attorney General's office, VWGoA disclosed that a vendor left unsecured data exposed on the Internet between August 2019 and May 2021.
On March 20th, VWGoA was notified by the vendor that an unauthorized person had accessed the data and may have obtained the customer information for Audi, Volkswagen, and some authorized dealers.
VWGoA states that the breach involved 3.3 million customers, with over 97% of those affected relating to Audi customers and interested buyers.
The data exposed varies per customer but could range from contact information to more sensitive information such as social security numbers and loan numbers.
"The data included some or all of the following contact information about you: first and last name, personal or business mailing address, email address, or phone number. In some instances, the data also included information about a vehicle purchased, leased, or inquired about, such as the Vehicle Identification Number (VIN), make, model, year, color, and trim packages," explains the VWGoA data breach notification first reported by TechCrunch.
"The data also included more sensitive information relating to eligibility for a purchase, loan, or lease. More than 95% of the sensitive data included was driver’s license numbers. There were also a very small number of dates of birth, Social Security or social insurance numbers, account or loan numbers, and tax identification numbers."
For those customers 90,000 customers who had more sensitive information exposed, Volkswagen is providing free credit protection and monitoring services, including $1 million of insurance against identity theft.
VWGoA began notifying affected customers and prospective customers yesterday via mail and warn that customers should be on the lookout for suspicious emails, calls, or texts.
Audi, Volkswagen data breach affects 3.3 million customers
-
16-06-2021, 12:40 AM #1023
-
16-06-2021, 04:43 AM #1024
Did buttplug ever rise to the challenge and hack Harrys passwords ?
-
16-06-2021, 12:49 PM #1025
Thread Information
Users Browsing this Thread
There are currently 9 users browsing this thread. (0 members and 9 guests)




 Reply With Quote
Reply With Quote
